Network Assessments: The Why, What, & How to Identify Weaknesses
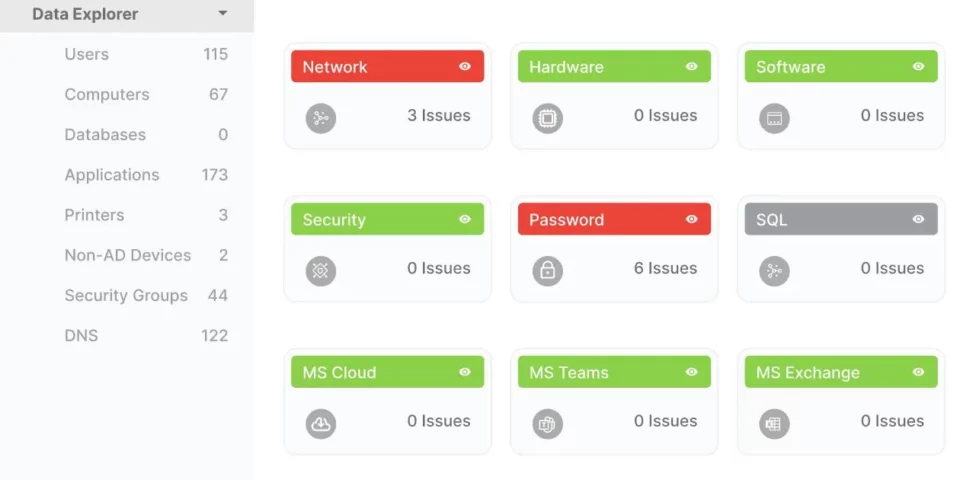
In this blog we’ll cover the importance of network assessments, how it’s conducted, the insights you’ll receive, and how to request one.
How to Recycle Computer Hardware: Protect Yourself & The Planet

Don’t discard old computer hardware by throwing it out. Instead, consider destroying or recycling to ensure important data is wiped off and limit e-waste.
3 Major Mistakes to Avoid in Disaster Recovery Planning

Read the 3 biggest mistakes companies make when preparing disaster recovery and data recovery plans. Don’t let a disaster disrupt your business continuity.
Password Best Practices: The Do’s and Don’ts
Password Security is As Critical as Ever Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo. A staggering 80% of security breaches are traced back to compromised passwords—that are either stolen, reused, or weak. This statistic uncovered by LastPass is alarming for business owners and equally […]
4 Important Ways to Improve Data Security

Security isn’t inherently convenient. If it’s easy, it might not be secure. Stay ahead of hackers with our top data security tips.
