Cybersecurity Services
Looking for
A Provider that Prioritizes Cybersecurity?
Partner with Prime Secured to Protect Your Data
Choosing the right IT provider means prioritizing a cybersecurity-first approach. At our core, we believe that a powerful defense is non-negotiable, which is why our solutions are indivisible. We don’t allow for the removal of any security measures because to do so would compromise your protection. Our technology stack is meticulously configured with cybersecurity as its cornerstone. Our decisions aren’t swayed by cost; instead, they’re driven by the efficacy of each technology’s cyber defenses. This commitment offers our clients additional peace of mind, knowing their solutions are crafted for maximum security. Explore everything our cybersecurity services offer.
Are you protected from a ransomware attack?
Download your ransomware survival guide and learn trends, impact, prevention, and how to respond to a ransomware attack.
Prime Secured for Cybersecurity Services
The market is flooded with Managed Service Providers, but identifying one that truly possesses the knowledge to educate, prioritize, and understand both current and emerging threats is a challenge. It takes a provider with exceptional expertise and credibility. Discover our core cybersecurity offerings, where our commitment to your security is clear.
24x7 Firewall Monitoring
Our firewall monitoring service works tirelessly to protect your network’s gateway, preventing unauthorized access and defending against external threats. With real-time threat detection and rapid response, you can focus on your business, knowing your data is secure.
24x7 Endpoint Monitoring
Endpoints are often the target of attacks. Our round-the-clock monitoring ensures every device connected to your network is secure. From laptops to mobile devices, we keep your endpoints patched and protected against the latest threats.
Dark Web Monitoring
Sensitive information can end up on the dark web. Our dark web monitoring service continuously scans dark web forums and marketplaces for your business’s data, alerting you to potential leaked information so you can take action immediatley.
Advanced Email Protection
Email is a common channel for phishing and malware. Our advanced email protection filters out dangerous emails before they reach your inbox, using sophisticated algorithms to detect and quarantine threats.
Secure Remote Capabilities
Empower your team to work from anywhere without compromising security. Our secure remote capabilities ensure that your employees can access your network safely, no matter where they are, with features like VPNs, secure file sharing, mobile device management and multi-factor authentication.
Vulnerability Assessment & Penetration Testing
Available as an add-on service upon request, this dual approach identifies vulnerabilities within your network and applications, then tests these weaknesses under controlled conditions to simulate potential attacks. By exposing and addressing these gaps, we strengthen your defenses against real-world cyber threats.
The Importance of Cybersecurity and Data Protection
Understand the prevalence of cybersecurity attacks and their potential impact on your organization.
Secure Your Business Now with Our Cybersecurity Services
Trending
Cybersecurity Topics
You Might be Interested in
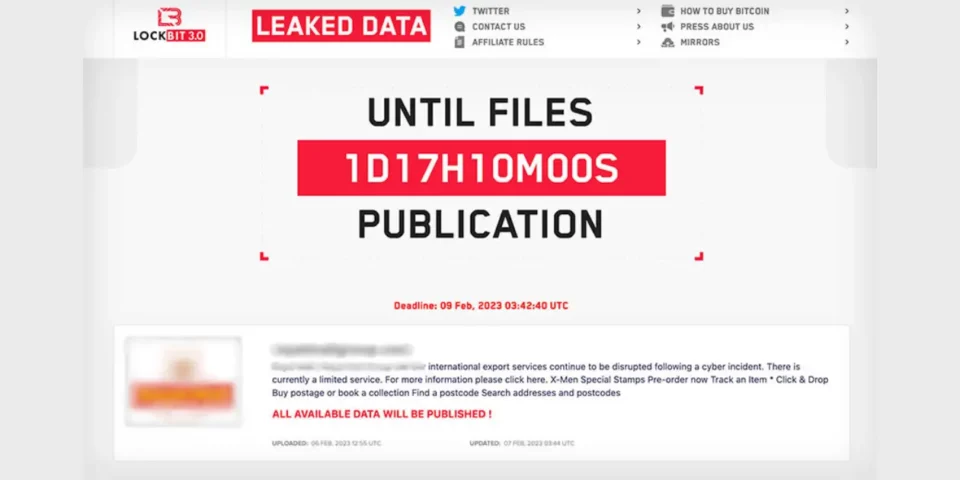
Protect Against Ransomware as a Service Groups: Basic to Advanced Steps