Complimentary Network Security Assessment
Curious to Know the State of Your IT Infrastructure?
Find out with a complimentary network assessment conducted by Prime Secured professionals
Insights we uncover:
- Network Architecture
- Hardware & Software Inventory
- Cybersecurity Posture
- Performance Analysis
- Compliance with Standards & Policies
- User Experience & Satisfaction
Inquire About Your Free Network Assessment
The Importance of Evaluating Your Network
Getting a network check-up, or assessment, is key to ensuring your organization’s IT infrastructure operates at its best, is secure, and is reliable. We’ll look closely at how your network is currently functioning, identifying any weak spots, slow points, or setup mistakes that could lead to problems, such as system crashes, security risks, or other slowdowns. Even if you already have a tech support team or service provider managing your network, having a separate IT audit can be very eye-opening. We have conducted network assessments and found that businesses often think everything with their network is fine, but our audit reveals there are significant issues that have been overlooked.
Findings from over 30 Assessments from Companies with an Existing MSP
What's Included in Your Network Audit Report?
The information you'll recieve in a report format:
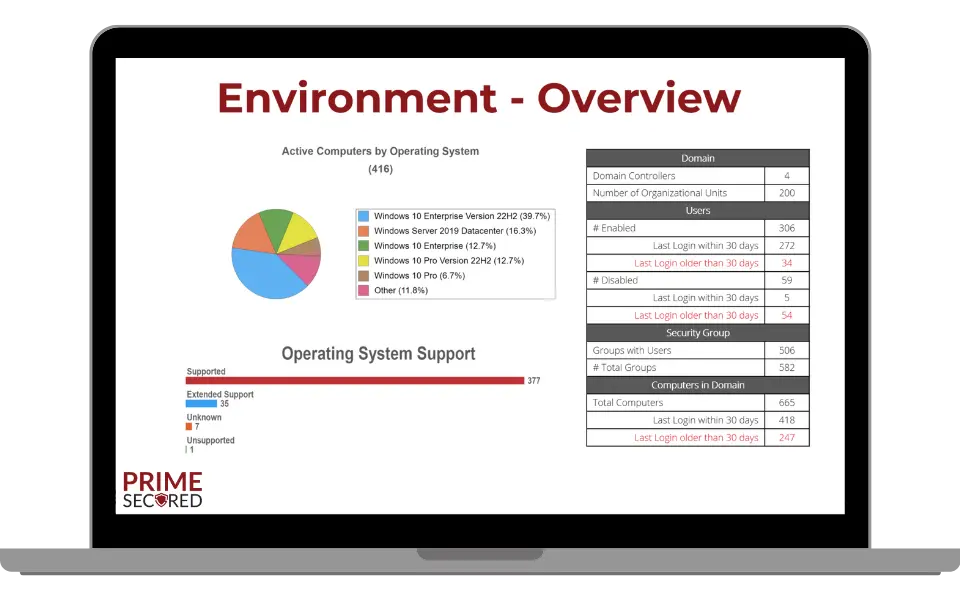
- Network Environment Overview
- Asset Summary
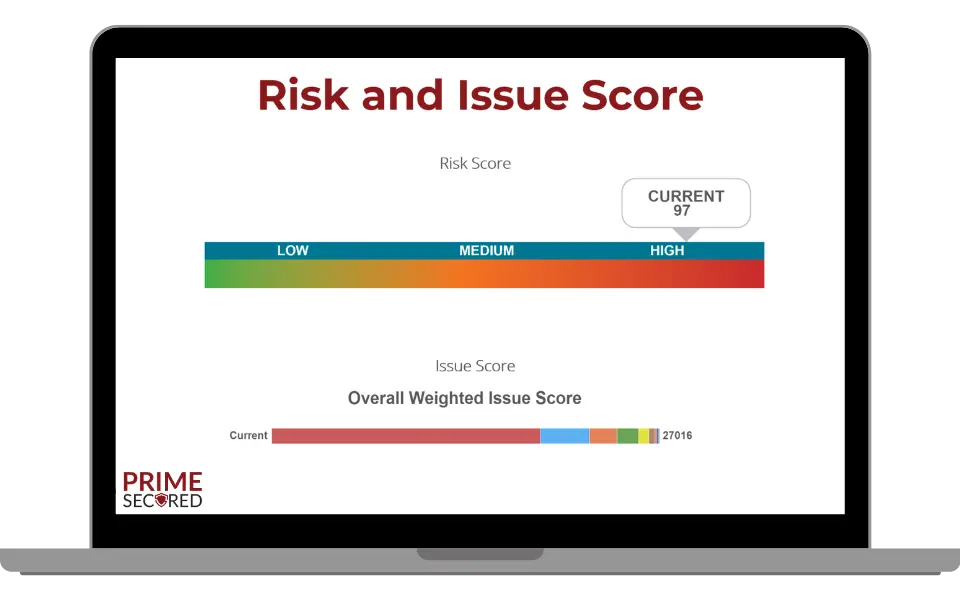
- Risk & Issue Score
- Review of Each Issue
- Recommendations
The Ultimate Guide to Complimentary Network Assessments by Prime Secured
In today’s hyper-connected business environment, maintaining a secure, high-performing network is no longer optional—it’s a necessity. Prime Secured offers a complimentary network assessment to help organizations identify network problems, optimize performance, and strengthen security posture. This in-depth guide explores everything you need to know about network security assessments, why they matter, and how they can transform your IT environment.What Is a Network Assessment?
A network assessment is a comprehensive evaluation of an organization’s network infrastructure, including network devices, traffic flow, security controls, and key network metrics. It provides a deep understanding of your IT environment, uncovering network vulnerabilities, inefficiencies, and opportunities for improvement.Why Perform a Network Assessment?
Organizations conduct network security risk assessments to:- Identify network problems affecting network speed, uptime, and reliability
- Detect security risks such as weak passwords, outdated software, or misconfigured firewall rules
- Optimize performance by analyzing bandwidth usage, memory usage, and traffic patterns
- Ensure compliance with regulatory compliance requirements
- Gain insights into how many users rely on the network and their usage patterns
- Support strategic business decisions with historical performance data
- Security breaches due to unidentified network vulnerabilities
- Poor network performance leading to lost productivity
- Inadequate bandwidth causing slowdowns during peak hours
- Non-compliance with industry regulations
What Does a Network Assessment Cover?
Prime Secured’s network security assessment evaluates multiple aspects of your network health, including security, performance, and scalability.1. Network Security Risk Assessment
A vulnerability assessment is critical to identify potential vulnerabilities before cybercriminals exploit them. Our assessment includes:- Reviewing access control lists (ACLs) and firewall rules
- Checking for weak passwords and inadequate security settings
- Scanning for outdated software and missing patches
- Detecting internal weaknesses that could lead to cyber attacks
- Optional penetration testing to simulate real-world threats
2. Network Performance & Health Check
A slow or unreliable network disrupts business operations. Our assessment analyzes:- Key network metrics (latency, jitter, packet loss)
- Network uptime and historical performance data
- Underused or overused resources (servers, switches, routers)
- Wireless networks for dead zones or interference
- Device configurations impacting efficiency
3. Network Topology & Device Inventory Mapping
Understanding your network topology is essential for troubleshooting and scaling. Our network assessment tool helps:- Automatically discover all network components (routers, switches, servers)
- Build a device inventory for better asset management
- Identify integration points that may cause bottlenecks
- Detect outdated firmware or unsupported hardware
4. Traffic & Bandwidth Analysis
Unmonitored network traffic can lead to:- Inadequate bandwidth during critical operations
- Downloading large files slowing down essential tasks
- Unauthorized data exfiltration
- Traffic flow to detect anomalies
- Usage patterns to optimize network resources
- Bandwidth allocation to prevent congestion
5. Compliance & Reporting
Many industries have strict regulatory compliance requirements. Our network assessment report helps:- Verify adherence to security measures (HIPAA, GDPR, PCI DSS)
- Generate reports for audits and informed decisions
- Document security posture for stakeholders
How Does a Network Assessment Work?
Step 1: Discovery Phase
Using automated tools, we scan your existing network to gather data on:- Network devices (routers, switches, firewalls)
- Operating system versions and patches
- Device configurations and security settings
Step 2: Analysis Phase
Our experts review:- Network vulnerabilities and security risks
- Historical performance data to detect trends
- Memory usage, CPU load, and traffic flow inefficiencies
Step 3: Reporting Phase
You receive a network assessment report detailing:- Identified network problems
- Security gaps and remediation steps
- Recommendations to optimize performance
Step 4: Action Plan
We help implement fixes, such as:- Upgrading outdated software
- Adjusting firewall rules and access control lists
- Enabling continuous monitoring for real-time alerts
Key Benefits of a Network Assessment
1. Enhanced Security Posture
- Prevents cyber attacks by identifying vulnerabilities
- Strengthens security controls and access management
2. Improved Network Performance
- Resolves inadequate bandwidth and network speed issues
- Eliminates bottlenecks in traffic flow
3. Cost Savings & Efficiency
- Avoids unnecessary hardware upgrades by right-sizing network resources
- Reduces downtime with proactive network monitoring
4. Regulatory Compliance
- Ensures adherence to regulatory compliance requirements
- Provides documentation for audits
5. Scalability & Future Growth
- Prepares network infrastructure for expansion
- Supports strategic business decisions with data-driven insights
Who Needs a Network Assessment?
- Businesses experiencing slow network speed or frequent outages
- Companies concerned about cyber threats and data breaches
- Organizations planning IT infrastructure upgrades
- IT departments needing continuous monitoring
